一、前因
2026 年 2 月 27 日附近,有大量消息来源12345表示青龙面板出现 0 day 漏洞,我 VPS 虽然没有用青龙面板,但是平日里的防护也是比较弱,借此机会加强一下对服务器的防护
注:青龙面板已于 2026 年 3 月 1 日 的 v2.20.2 版中已修复该 0 day 漏洞
Terminal window
漏洞摘要
青龙面板 v2.20.1 及以下版本存在多个安全漏洞,这些漏洞组合利用可导致 未授权远程代码执行(Unauthenticated RCE)。
核心问题是 JWT 签名密钥使用了硬编码的默认值 'whyour-secret',该值在开源代码中公开可见。攻击者无需任何凭据即可伪造有效的 JWT Token,调用后端 API 向 config.sh 注入恶意 Shell 脚本。由于 config.sh 在每次定时任务执行前被 source 加载,恶意代码得以持久化执行。
实际攻击中,恶意载荷从外部服务器下载加密货币挖矿程序(.fullgc),在后台运行并消耗大量系统资源(CPU 占用率达 85%-100%)。
二、开始排查
主要步骤还是从 SSH ---> 系统性能 ---> 自启动 开始排查
1. SSH
SSH 的话,因为根据 【自用】VPS 到手后必做的几件事↗ 部署的(自己的教程就是好用) 的话,默认 SSH 端口是非默认+ SSH 密钥登陆 + root 用户不可直接登录 + fail2ban 是部署了的
所以我们这次只需要查看一下:
- SSH 登录历史
- SSH 认证日志
fail2ban是否有有效工作
即可
我们一个一个来
1.1 SSH 登录历史
# 查看最近成功登录的 50 条登录历史last -a | head -n 50# 查看最近失败登录的 50 条登录历史sudo lastb -a | head -n 50如果此时出现 找不到
last和lastb命令的情况下,可以尝试安装wtmpdb包Terminal window 然后再去测试就会发现有命令
last了而
lastb命令就只能用日志检索来代替Terminal window 这个是统计失败来源 IP
成功登录
Terminal window $ last -a | head -n 50moka pts/0 Mon Mar 2 20:30 still logged in 223.***.***.***moka pts/1 Mon Mar 2 16:33 - 16:40 (00:07) :pts/0:S.0moka pts/0 Mon Mar 2 16:16 - 18:49 (02:32) 223.***.***.***moka pts/0 Sun Mar 1 19:01 - 19:14 (00:12) 223.***.***.***moka pts/0 Fri Feb 27 12:26 - 13:26 (00:59) 112.***.***.***moka pts/0 Fri Feb 27 08:02 - 08:03 (00:00) 112.***.***.***root pts/0 Thu Feb 26 12:28 - 15:34 (03:05) 112.***.***.***moka pts/0 Thu Feb 26 11:42 - 11:51 (00:08) 112.***.***.***moka pts/0 Tue Feb 24 13:59 - 15:53 (01:53) 112.***.***.***moka pts/1 Mon Feb 23 11:11 - 11:18 (00:06) :pts/0:S.0moka pts/0 Mon Feb 23 11:11 - 12:10 (00:59) 112.***.***.***moka pts/0 Mon Feb 23 10:07 - 10:11 (00:04) 112.***.***.***reboot system boot Mon Feb 23 09:53 still running 6.8.0-100-genericmoka pts/0 Fri Feb 20 09:53 - 12:36 (02:42) 112.***.***.***moka pts/0 Fri Feb 20 09:06 - 09:07 (00:00) 112.***.***.***moka pts/0 Wed Feb 18 18:04 - 18:05 (00:00) 112.***.***.***moka pts/0 Wed Feb 18 11:41 - 11:41 (00:00) 45.***.***.***moka pts/5 Mon Feb 16 12:49 - 12:50 (00:01) 112.***.***.***moka pts/4 Mon Feb 16 12:48 - 12:50 (00:01) 112.***.***.***moka pts/3 Mon Feb 16 11:46 - 12:50 (01:04) 112.***.***.***moka pts/0 Mon Feb 16 11:45 - 12:50 (01:04) 112.***.***.***moka pts/0 Mon Feb 16 08:24 - 10:57 (02:33) 112.***.***.***moka pts/7 Sun Feb 15 17:12 - 18:16 (01:03) 112.***.***.***moka pts/6 Sun Feb 15 17:06 - 19:50 (02:44) 112.***.***.***moka pts/6 Sun Feb 15 17:01 - 17:06 (00:04) 112.***.***.***moka pts/5 Sun Feb 15 16:56 - 19:40 (02:44) 112.***.***.***moka pts/4 Sun Feb 15 16:56 - 19:40 (02:44) 112.***.***.***moka pts/3 Sun Feb 15 15:22 - 19:34 (04:12) 112.***.***.***moka pts/2 Sun Feb 15 14:40 - 19:34 (04:53) 112.***.***.***moka pts/0 Sun Feb 15 14:40 - 19:34 (04:54) 112.***.***.***moka pts/2 Sun Feb 15 14:24 - 14:40 (00:15) 112.***.***.***moka pts/0 Sun Feb 15 14:03 - 14:40 (00:36) 112.***.***.***moka pts/1 Sun Feb 15 09:53 - 09:56 (00:03) :pts/0:S.0moka pts/0 Sun Feb 15 09:47 - 09:56 (00:09) 112.***.***.***moka pts/2 Sat Feb 14 16:27 - 20:13 (03:45) 112.***.***.***moka pts/0 Sat Feb 14 12:56 - 20:13 (07:16) 112.***.***.***moka pts/0 Sat Feb 14 10:24 - 10:26 (00:02) 112.***.***.***moka pts/0 Sat Feb 14 10:23 - 10:23 (00:00) 112.***.***.***moka pts/0 Fri Feb 13 07:05 - 07:13 (00:07) 112.***.***.***moka pts/1 Thu Feb 12 06:20 - 06:21 (00:01) :pts/0:S.0moka pts/0 Thu Feb 12 06:20 - 06:21 (00:01) 112.***.***.***reboot system boot Thu Feb 12 06:12 still running 6.8.0-100-genericmoka pts/2 Mon Feb 9 20:35 - 20:36 (00:01) :pts/0:S.0moka pts/2 Mon Feb 9 20:27 - 20:27 (00:00) :pts/0:S.0moka pts/0 Mon Feb 9 20:27 - 20:38 (00:10) 112.***.***.***moka pts/2 Mon Feb 9 10:35 - 10:36 (00:01) :pts/0:S.0moka pts/2 Mon Feb 9 10:29 - 10:29 (00:00) :pts/0:S.0moka pts/1 Mon Feb 9 10:29 - 10:29 (00:00) :pts/0:S.0moka pts/2 Mon Feb 9 10:29 - 10:29 (00:00) :pts/0:S.0moka pts/0 Mon Feb 9 10:28 - 13:59 (03:30) 112.***.***.***这上面出现的
223.***.***.***,112.***.***.***和45.***.***.***都是我自己的 IP 地址,而:pts/0:S.0则是伪终端,根据时间判断,应该是当时的复制终端,所以无事发生失败登录
Terminal window $ $ sudo lastb -a | head -n 50vyr_odoo ssh:notty Mon Mar 2 20:29 - 20:29 (00:00) 195.24.237.3hive ssh:notty Mon Mar 2 19:46 - 19:46 (00:00) 195.24.237.3mysql ssh:notty Mon Mar 2 19:31 - 19:31 (00:00) 195.24.237.3dudu ssh:notty Mon Mar 2 18:17 - 18:17 (00:00) 195.24.237.3admin ssh:notty Mon Mar 2 16:05 - 16:05 (00:00) 195.24.237.3student ssh:notty Mon Mar 2 14:36 - 14:36 (00:00) 195.24.237.3openeule ssh:notty Mon Mar 2 14:22 - 14:22 (00:00) 195.24.237.3oracle ssh:notty Mon Mar 2 14:07 - 14:07 (00:00) 195.24.237.3test ssh:notty Mon Mar 2 13:22 - 13:22 (00:00) 195.24.237.3alarm ssh:notty Mon Mar 2 12:53 - 12:53 (00:00) 195.24.237.3ubuntu ssh:notty Mon Mar 2 12:38 - 12:38 (00:00) 195.24.237.3teamhd ssh:notty Mon Mar 2 11:59 - 11:59 (00:00) 195.24.237.3teacher ssh:notty Mon Mar 2 08:20 - 08:20 (00:00) 195.24.237.3gas ssh:notty Mon Mar 2 05:44 - 05:44 (00:00) 195.24.237.3test ssh:notty Mon Mar 2 03:51 - 03:51 (00:00) 195.24.237.3ztl ssh:notty Sun Mar 1 09:44 - 09:44 (00:00) 195.24.237.3odin ssh:notty Sun Mar 1 03:44 - 03:44 (00:00) 195.24.237.3www ssh:notty Sun Mar 1 02:41 - 02:41 (00:00) 195.24.237.3可以看到此时
195.24.237.3这个 IP 在来回尝试登录我的 VPS,而我之前fail2ban设置的频率是 300s 内尝试次数超过 5 次就封禁,虽然这个次数没到,但是我们可以手动封禁,这个后面再说,我们先把这个 IP 记录一下
1.2 SSH 认证日志
# 查看最近登录sudo grep -E "sshd|Accepted|Failed|Invalid|authentication failure" /var/log/auth.log | tail -n 200# 快速统计成功登录来自哪些 IPsudo grep -E "sshd.*Accepted" /var/log/auth.log \| awk '{for(i=1;i<=NF;i++) if($i=="from") {print $(i+1); break}}' \| sort | uniq -c | sort -nr | head最近登录
Terminal window $ sudo grep -E "sshd|Accepted|Failed|Invalid|authentication failure" /var/log/auth.log | tail -n 2002026-03-01T00:05:49.909592+08:00 HK4C sshd[1517009]: Connection closed by authenticating user root 195.24.237.3 port 11760 [preauth]2026-03-01T00:21:23.132016+08:00 HK4C sshd[1519362]: Connection closed by authenticating user root 195.24.237.3 port 29688 [preauth]2026-03-01T02:41:40.538107+08:00 HK4C sshd[1540451]: Invalid user www from 195.24.237.3 port 172642026-03-01T02:41:40.807143+08:00 HK4C sshd[1540451]: Connection closed by invalid user www 195.24.237.3 port 17264 [preauth]2026-03-01T03:44:10.774123+08:00 HK4C sshd[1549789]: Invalid user odin from 195.24.237.3 port 238922026-03-01T03:44:11.592459+08:00 HK4C sshd[1549789]: Connection closed by invalid user odin 195.24.237.3 port 23892 [preauth]2026-03-01T07:06:47.388569+08:00 HK4C sshd[1580388]: Connection closed by authenticating user root 195.24.237.3 port 32092 [preauth]2026-03-01T08:29:33.702026+08:00 HK4C sshd[1592811]: Connection closed by authenticating user root 195.24.237.3 port 5772 [preauth]2026-03-01T09:44:13.181322+08:00 HK4C sshd[1604035]: Invalid user ztl from 195.24.237.3 port 575422026-03-01T09:44:14.627876+08:00 HK4C sshd[1604035]: Connection closed by invalid user ztl 195.24.237.3 port 57542 [preauth]2026-03-01T09:58:52.352421+08:00 HK4C sshd[1606239]: Connection closed by authenticating user root 195.24.237.3 port 62492 [preauth]2026-03-01T11:13:09.141928+08:00 HK4C sshd[1617389]: Connection closed by authenticating user root 195.24.237.3 port 39912 [preauth]2026-03-01T11:27:46.384227+08:00 HK4C sshd[1619604]: Connection closed by authenticating user root 195.24.237.3 port 39300 [preauth]2026-03-01T11:45:32.439144+08:00 HK4C sshd[1622280]: Connection closed by 162.216.150.126 port 518052026-03-01T12:41:42.805076+08:00 HK4C sshd[1630681]: Connection closed by authenticating user root 195.24.237.3 port 43872 [preauth]2026-03-01T19:00:01.603015+08:00 HK4C sshd[1688151]: Connection closed by authenticating user root 198.***.***.*** port 45952 [preauth]2026-03-01T19:00:56.501398+08:00 HK4C sshd[1688278]: Accepted publickey for moka from 223.***.***.*** port 2701 ssh2: ED25519 SHA256:5w**********z/ps**********Wck2026-03-01T19:00:56.507930+08:00 HK4C sshd[1688278]: pam_unix(sshd:session): session opened for user moka(uid=1000) by moka(uid=0)2026-03-01T19:03:35.431977+08:00 HK4C sshd[1689207]: Accepted publickey for root from 198.***.***.*** port 44292 ssh2: ED25519 SHA256:M5/HoOCZWxWFfya3qORWGjYRIYQ1Ju++D1HhVsBZjhc2026-03-01T19:03:35.433798+08:00 HK4C sshd[1689207]: pam_unix(sshd:session): session opened for user root(uid=0) by root(uid=0)2026-03-01T19:03:36.587454+08:00 HK4C sshd[1689207]: Received disconnect from 198.***.***.*** port 44292:11: disconnected by user2026-03-01T19:03:36.587766+08:00 HK4C sshd[1689207]: Disconnected from user root 198.***.***.*** port 442922026-03-01T19:03:36.587864+08:00 HK4C sshd[1689207]: pam_unix(sshd:session): session closed for user root2026-03-01T19:14:28.522767+08:00 HK4C sshd[1688382]: Received disconnect from 223.***.***.*** port 2701:11:2026-03-01T19:14:28.524773+08:00 HK4C sshd[1688382]: Disconnected from user moka 223.***.***.*** port 27012026-03-01T19:14:28.525185+08:00 HK4C sshd[1688278]: pam_unix(sshd:session): session closed for user moka2026-03-01T22:28:22.456857+08:00 HK4C sshd[1720019]: Connection closed by 162.216.150.43 port 501342026-03-02T00:33:53.802458+08:00 HK4C sshd[1738823]: Connection closed by 206.168.34.211 port 45430 [preauth]2026-03-02T03:51:50.156282+08:00 HK4C sshd[1769227]: Invalid user test from 195.24.237.3 port 577402026-03-02T03:51:50.754064+08:00 HK4C sshd[1769227]: Connection closed by invalid user test 195.24.237.3 port 57740 [preauth]2026-03-02T05:44:51.195391+08:00 HK4C sshd[1786167]: Invalid user gas from 195.24.237.3 port 375982026-03-02T05:44:51.562464+08:00 HK4C sshd[1786167]: Connection closed by invalid user gas 195.24.237.3 port 37598 [preauth]2026-03-02T07:02:45.141816+08:00 HK4C sshd[1797977]: Connection closed by authenticating user root 195.24.237.3 port 32906 [preauth]2026-03-02T08:20:36.620457+08:00 HK4C sshd[1809753]: Invalid user teacher from 195.24.237.3 port 368242026-03-02T08:20:36.952218+08:00 HK4C sshd[1809753]: Connection closed by invalid user teacher 195.24.237.3 port 36824 [preauth]2026-03-02T08:36:03.842457+08:00 HK4C sshd[1812057]: Connection closed by authenticating user root 195.24.237.3 port 36808 [preauth]2026-03-02T08:51:23.089987+08:00 HK4C sshd[1814410]: Connection closed by authenticating user root 195.24.237.3 port 60484 [preauth]2026-03-02T10:08:47.452441+08:00 HK4C sshd[1825998]: Connection closed by 35.203.211.62 port 517232026-03-02T10:41:31.749172+08:00 HK4C sshd[1830938]: Connection closed by authenticating user nobody 195.24.237.3 port 60016 [preauth]2026-03-02T11:59:18.170138+08:00 HK4C sshd[1842611]: Invalid user teamhd from 195.24.237.3 port 345562026-03-02T11:59:19.405415+08:00 HK4C sshd[1842611]: Connection closed by invalid user teamhd 195.24.237.3 port 34556 [preauth]2026-03-02T12:23:09.728405+08:00 HK4C sshd[1846196]: Connection closed by authenticating user root 195.24.237.3 port 44956 [preauth]2026-03-02T12:38:11.988193+08:00 HK4C sshd[1848447]: Invalid user ubuntu from 195.24.237.3 port 533642026-03-02T12:38:13.263538+08:00 HK4C sshd[1848447]: Connection closed by invalid user ubuntu 195.24.237.3 port 53364 [preauth]2026-03-02T12:53:10.336572+08:00 HK4C sshd[1850666]: Invalid user alarm from 195.24.237.3 port 553162026-03-02T12:53:11.658916+08:00 HK4C sshd[1850666]: Connection closed by invalid user alarm 195.24.237.3 port 55316 [preauth]2026-03-02T13:08:04.632588+08:00 HK4C sshd[1852920]: Connection closed by authenticating user root 195.24.237.3 port 34590 [preauth]2026-03-02T13:22:54.745066+08:00 HK4C sshd[1855167]: Invalid user test from 195.24.237.3 port 386522026-03-02T13:22:56.015314+08:00 HK4C sshd[1855167]: Connection closed by invalid user test 195.24.237.3 port 38652 [preauth]2026-03-02T13:37:43.535381+08:00 HK4C sshd[1857336]: Connection closed by authenticating user root 195.24.237.3 port 48422 [preauth]2026-03-02T13:52:35.213450+08:00 HK4C sshd[1859598]: Connection closed by authenticating user root 195.24.237.3 port 52204 [preauth]2026-03-02T14:07:21.586690+08:00 HK4C sshd[1861807]: Invalid user oracle from 195.24.237.3 port 607462026-03-02T14:07:23.280541+08:00 HK4C sshd[1861807]: Connection closed by invalid user oracle 195.24.237.3 port 60746 [preauth]2026-03-02T14:22:09.330402+08:00 HK4C sshd[1864070]: Invalid user openeuler from 195.24.237.3 port 456062026-03-02T14:22:10.643950+08:00 HK4C sshd[1864070]: Connection closed by invalid user openeuler 195.24.237.3 port 45606 [preauth]2026-03-02T14:36:50.573879+08:00 HK4C sshd[1866257]: Invalid user student from 195.24.237.3 port 426842026-03-02T14:36:51.967831+08:00 HK4C sshd[1866257]: Connection closed by invalid user student 195.24.237.3 port 42684 [preauth]2026-03-02T15:50:58.562564+08:00 HK4C sshd[1877392]: Connection closed by authenticating user root 195.24.237.3 port 51514 [preauth]2026-03-02T16:05:36.409063+08:00 HK4C sshd[1879575]: Invalid user admin from 195.24.237.3 port 370782026-03-02T16:05:37.913296+08:00 HK4C sshd[1879575]: Connection closed by invalid user admin 195.24.237.3 port 37078 [preauth]2026-03-02T16:16:31.875608+08:00 HK4C sshd[1881239]: Accepted publickey for moka from 223.***.***.*** port 2564 ssh2: ED25519 SHA256:5w**********z/ps**********Wck2026-03-02T16:16:31.878600+08:00 HK4C sshd[1881239]: pam_unix(sshd:session): session opened for user moka(uid=1000) by moka(uid=0)2026-03-02T16:20:16.423716+08:00 HK4C sshd[1882203]: Connection closed by authenticating user root 195.24.237.3 port 45258 [preauth]2026-03-02T16:34:53.258926+08:00 HK4C sshd[1884387]: Connection closed by authenticating user root 195.24.237.3 port 38348 [preauth]2026-03-02T16:46:58.867674+08:00 HK4C sudo: moka : TTY=pts/0 ; PWD=/home/moka ; USER=root ; COMMAND=/usr/bin/grep -E 'sshd|Accepted|Failed|Invalid|authentication failure' /var/log/auth.log2026-03-02T16:49:33.084634+08:00 HK4C sshd[1886636]: Connection closed by authenticating user root 195.24.237.3 port 56224 [preauth]2026-03-02T16:51:12.279174+08:00 HK4C sudo: moka : TTY=pts/0 ; PWD=/home/moka ; USER=root ; COMMAND=/usr/bin/fail2ban-client status sshd2026-03-02T16:51:41.824433+08:00 HK4C sudo: moka : TTY=pts/0 ; PWD=/home/moka ; USER=root ; COMMAND=/usr/bin/fail2ban-client set sshd banip 195.24.237.32026-03-02T16:51:48.820889+08:00 HK4C sudo: moka : TTY=pts/0 ; PWD=/home/moka ; USER=root ; COMMAND=/usr/bin/fail2ban-client status sshd2026-03-02T17:04:09.417037+08:00 HK4C sshd[1888914]: Connection closed by authenticating user root 195.24.237.3 port 55476 [preauth]2026-03-02T18:17:49.993373+08:00 HK4C sshd[1899904]: Invalid user dudu from 195.24.237.3 port 402222026-03-02T18:17:51.631989+08:00 HK4C sshd[1899904]: Connection closed by invalid user dudu 195.24.237.3 port 40222 [preauth]2026-03-02T18:49:24.780768+08:00 HK4C sshd[1881319]: Received disconnect from 223.***.***.*** port 2564:11:2026-03-02T18:49:24.782493+08:00 HK4C sshd[1881319]: Disconnected from user moka 223.***.***.*** port 25642026-03-02T18:49:24.782928+08:00 HK4C sshd[1881239]: pam_unix(sshd:session): session closed for user moka2026-03-02T19:31:44.778402+08:00 HK4C sshd[1911262]: Invalid user mysql from 195.24.237.3 port 406282026-03-02T19:31:46.049998+08:00 HK4C sshd[1911262]: Connection closed by invalid user mysql 195.24.237.3 port 40628 [preauth]2026-03-02T19:46:19.158435+08:00 HK4C sshd[1913437]: Invalid user hive from 195.24.237.3 port 447562026-03-02T19:46:20.541793+08:00 HK4C sshd[1913437]: Connection closed by invalid user hive 195.24.237.3 port 44756 [preauth]2026-03-02T20:00:49.917286+08:00 HK4C sshd[1915635]: Connection closed by authenticating user root 195.24.237.3 port 44962 [preauth]2026-03-02T20:15:18.039603+08:00 HK4C sshd[1917833]: Connection closed by authenticating user root 195.24.237.3 port 52990 [preauth]2026-03-02T20:29:47.520061+08:00 HK4C sshd[1919999]: Invalid user vyr_odoo from 195.24.237.3 port 563562026-03-02T20:29:49.246996+08:00 HK4C sshd[1919999]: Connection closed by invalid user vyr_odoo 195.24.237.3 port 56356 [preauth]2026-03-02T20:30:07.449599+08:00 HK4C sshd[1920063]: Accepted publickey for moka from 223.***.***.*** port 2865 ssh2: ED25519 SHA256:5w**********z/ps**********Wck2026-03-02T20:30:07.452744+08:00 HK4C sshd[1920063]: pam_unix(sshd:session): session opened for user moka(uid=1000) by moka(uid=0)2026-03-02T20:44:20.094270+08:00 HK4C sshd[1922673]: Connection closed by authenticating user root 195.24.237.3 port 38112 [preauth]2026-03-02T20:49:01.214433+08:00 HK4C sudo: moka : TTY=pts/0 ; PWD=/home/moka ; USER=root ; COMMAND=/usr/bin/grep -E 'sshd|Accepted|Failed|Invalid|authentication failure' /var/log/auth.log2026-03-02T20:50:27.359177+08:00 HK4C sudo: moka : TTY=pts/0 ; PWD=/home/moka ; USER=root ; COMMAND=/usr/bin/grep Accepted /var/log/auth.log2026-03-02T20:51:19.528610+08:00 HK4C sudo: moka : TTY=pts/0 ; PWD=/home/moka ; USER=root ; COMMAND=/usr/bin/grep -E sshd.*Accepted /var/log/auth.log2026-03-02T20:58:50.124246+08:00 HK4C sshd[1924891]: Connection closed by authenticating user root 195.24.237.3 port 45930 [preauth]2026-03-02T21:02:53.469058+08:00 HK4C sudo: moka : TTY=pts/0 ; PWD=/home/moka ; USER=root ; COMMAND=/usr/bin/grep -E 'sshd|Accepted|Failed|Invalid|authentication failure' /var/log/auth.log可以发现还是上面的那些内容
最近成功登录是来自哪些 IP
Terminal window $ sudo grep -E "sshd.*Accepted" /var/log/auth.log \| awk '{for(i=1;i<=NF;i++) if($i=="from") {print $(i+1); break}}' \| sort | uniq -c | sort -nr | head3 223.***.***.***1 198.**.***.***前面的数字是次数,后面的是 IP,可以发现仍然是我们的 IP
在检测 fail2ban 之前,有一个小插曲,有一台机器在进行刚才 SSH 登录历史的时候发现有一个不是我的 IP
# last -a | head -n 50 | grep 134.75.145.90root pts/2 Thu Feb 26 04:24 - 04:24 (00:00) 134.75.145.90就是这个 IP: 134.75.145.90,而在进行 SSH 认证日志 测试的时候并未发现有这个 IP,这个是正常现象,因为这条记录可能在已轮转的日志里
last读的是 /var/log/wtmp(登录历史数据库),保存周期通常更久; 而/var/log/auth.log会被 logrotate 轮转成auth.log.1、auth.log.2.gz……你只查了当前auth.log,所以可能漏掉 2 月 26 日那条
所以此时需要我们全盘搜索:
# sudo zgrep -hE "sshd.*Accepted" /var/log/auth.log* | grep "134.75.145.90"Feb 26 04:24:01 vultr sshd[8546]: Accepted publickey for root from 134.75.145.90 port 52516 ssh2: ED25519 SHA256:6tOC2PKravofjFPcnzkuMjg++cxG3s07N98aIt3L7UYFeb 26 04:29:48 vultr sshd[8641]: Accepted publickey for root from 134.75.145.90 port 58004 ssh2: ED25519 SHA256:6tOC2PKravofjFPcnzkuMjg++cxG3s07N98aIt3L7UYFeb 26 04:30:53 vultr sshd[8721]: Accepted publickey for root from 134.75.145.90 port 51888 ssh2: ED25519 SHA256:6tOC2PKravofjFPcnzkuMjg++cxG3s07N98aIt3L7UY从日志里可以看出,134.75.145.90 这个 IP 在 2 月 26 日 04:24、04:29、04:30 使用 SSH 公钥的方式,以 root 身份登录了这台 VPS
因为是公钥泄露,所以我们需要找到是哪个公钥出现了泄露
# sudo ssh-keygen -lf /root/.ssh/authorized_keys | grep '6tOC2PKravofjFPcnzkuMjg++cxG3s07N98aIt3L7UY'256 SHA256:6tOC2PKravofjFPcnzkuMjg++cxG3s07N98aIt3L7UY root@JP1G (ED25519)经检查发现,是 JP1G 这台机器的公钥进行泄露,那么先要立刻从服务器上移除这把泄露 key,并且替换这个密钥
# 在 JP1Gssh-keygen -t ed25519cat ~/.ssh/id_ed25519.pub# 在其他机器vim ~/.ssh/authorized_keys# 粘贴在 JP1G 上获得的公钥1.3 fail2ban 是否有有效工作
如果是根据我 【自用】VPS 到手后必做的几件事↗ 教程来的话,那么 jail 应该就是默认的 sshd
# 查看 fail2ban 状态sudo fail2ban-client status# 具体到某个 jailsudo fail2ban-client status sshd# ban 掉 IP 1.2.3.4sudo fail2ban-client set sshd banip 1.2.3.4# 再次查看 jail 状态sudo fail2ban-client status sshd正如上面所言,现在有 195.24.237.3 和 124.237.79.34 来回扫机器,还有莫名的 134.75.145.90 来登录我的 VPS,那么这几个 IP 都是我们要着重封禁的
sudo fail2ban-client set sshd banip 195.24.237.3sudo fail2ban-client set sshd banip 124.237.79.34sudo fail2ban-client set sshd banip 134.75.145.90第二天早上发现 195.24.237.3 仍在尝试登录,真得控制你了.jpg
$ sudo lastb -a | head -n 50dbus ssh:notty Tue Mar 3 07:52 - 07:52 (00:00) 195.24.237.3root1 ssh:notty Tue Mar 3 07:37 - 07:37 (00:00) 195.24.237.3elastics ssh:notty Tue Mar 3 05:59 - 05:59 (00:00) 195.24.237.3ubuntu ssh:notty Tue Mar 3 05:27 - 05:27 (00:00) 195.24.237.3admin ssh:notty Tue Mar 3 00:46 - 00:46 (00:00) 195.24.237.3admin ssh:notty Mon Mar 2 23:13 - 23:13 (00:00) 195.24.237.3dixi ssh:notty Mon Mar 2 22:57 - 22:57 (00:00) 195.24.237.3此时昨晚的 ban list 已过期(因为之前设置的是 bantime = 600 是 600s 也就是 10 分钟),此时我们需要永久封禁,可以创建一个名为 recidive 的 jail
在 /etc/fail2ban/jail.local 加上
[recidive]enabled = truelogpath = /var/log/fail2ban.log# 在一天内findtime = 1d# 最多尝试 5 次maxretry = 5# 就被永久封禁bantime = -1然后重启 fail2ban 并查看状态
sudo systemctl restart fail2bansudo fail2ban-client status recidive$ sudo fail2ban-client status recidiveStatus for the jail: recidive|- Filter| |- Currently failed: 0| |- Total failed: 0| `- Journal matches: _SYSTEMD_UNIT=fail2ban.service PRIORITY=5`- Actions |- Currently banned: 0 |- Total banned: 0 `- Banned IP list:此时我们可以添加永久封禁的 IP
sudo fail2ban-client set recidive banip 195.24.237.3# 查看永久封禁的状态sudo fail2ban-client status recidive$ sudo fail2ban-client status recidiveStatus for the jail: recidive|- Filter| |- Currently failed: 0| |- Total failed: 0| `- Journal matches: _SYSTEMD_UNIT=fail2ban.service PRIORITY=5`- Actions |- Currently banned: 1 |- Total banned: 1 `- Banned IP list: 195.24.237.3可以看到,此时有一个 195.24.237.3 的 IP 被永久封禁
至此,SSH 排查结束
2. 系统性能
大致流程是:使用实时监控工具来看看谁在抢占资源 ---> 排查 CPU 负载 ---> 排查 磁盘 I/O ---> 排查网络连接是否有异常
2.1 快速全局概览:实时监控工具
首先,我们需要一个直观的界面来看看谁在抢占资源,比如 htop 或者 btop
观察重点:看 CPU 柱状图。如果某个进程持续占用 90%-100% 的 CPU,且进程名随机(如 ajk382)或伪装成系统进程(如 syslogd 但路径不对),就要警惕了
htop 使用技巧:按 P 按 CPU 排序,按 M 按内存排序
htop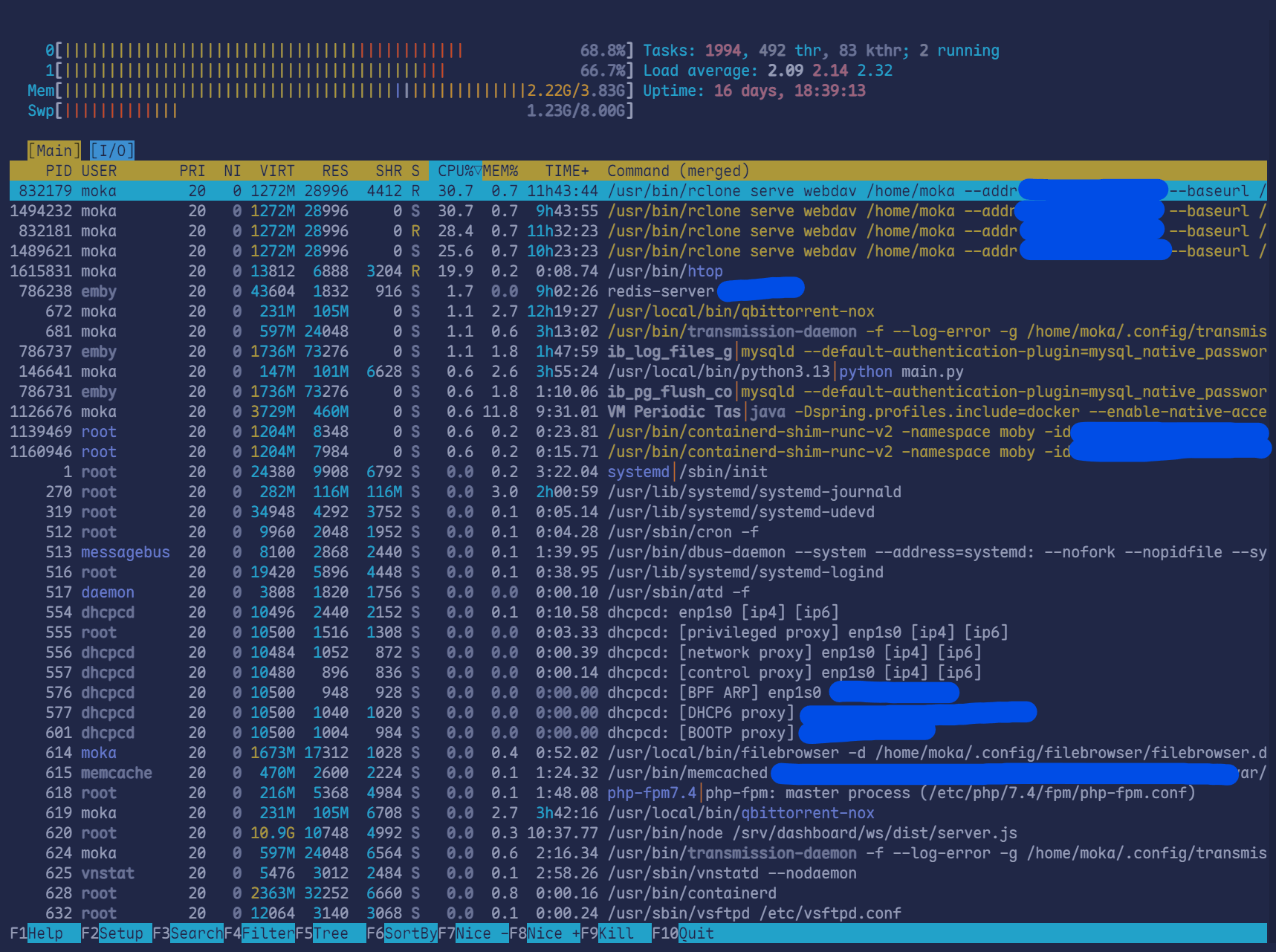
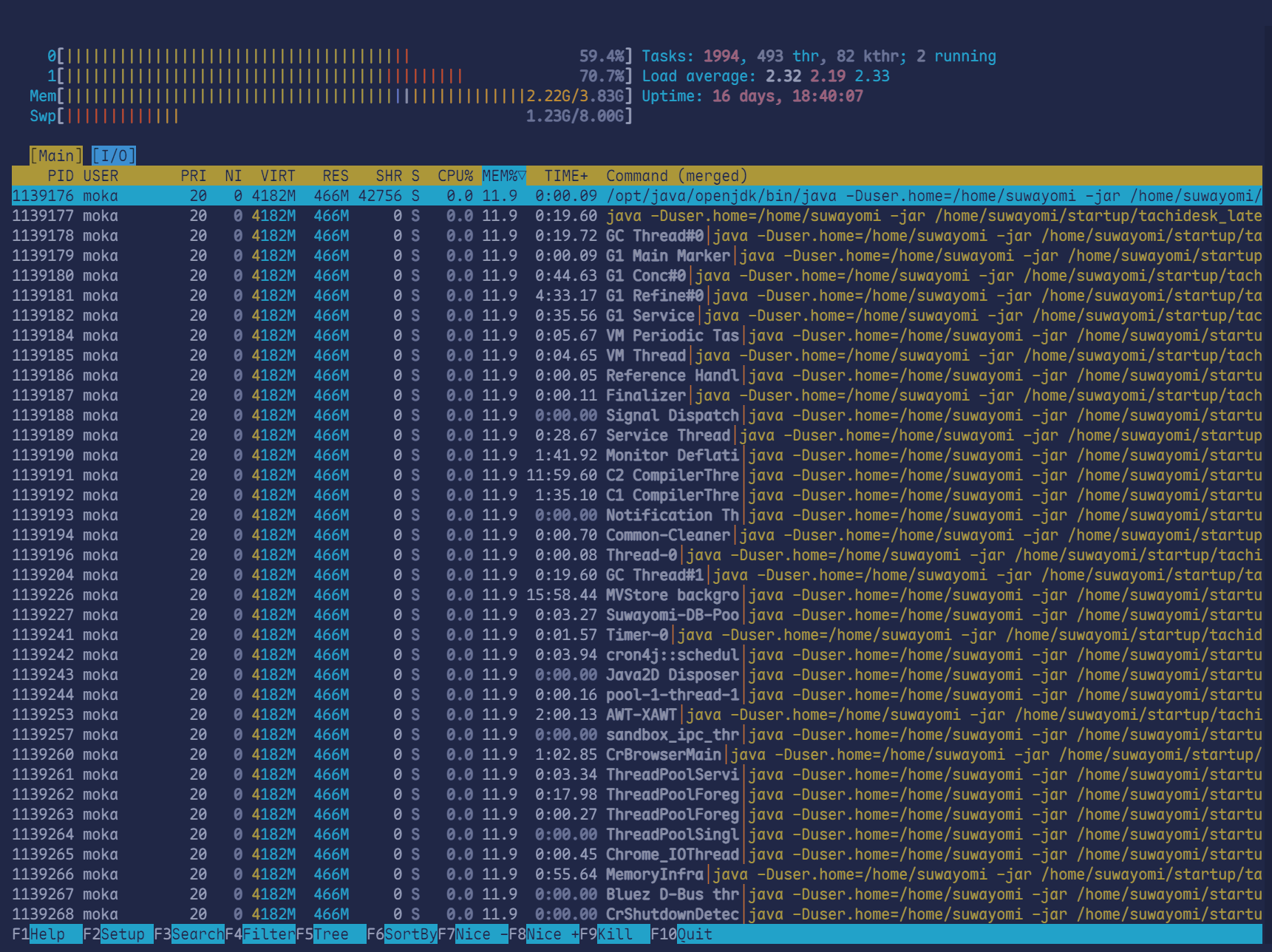
大致看了一眼,应该没有什么问题
2.2 CPU 负载
uptime这里主要看 Load Average:分别代表 1、5、15 分钟的平均负载。如果数值远超过你的 CPU 核心数(例如 4 核机器负载到了 10 以上),说明系统正处于高压状态
$ uptime 09:26:46 up 7 days, 23:33, 4 users, load average: 0.57, 0.52, 0.372.3 磁盘 I/O
iostat -x 1 5有时候矿机不费 CPU 费硬盘,或者木马在疯狂写日志
这里主要看 %util:如果某个磁盘利用率接近 100%,说明 I/O 达到瓶颈。
这里因为太长就不放了
2.4 网络是否异常
sudo netstat -antp这里看 IP 是否为境外 IP,端口是否为 3333, 4444, 5555, 8888 等,或者看有没有你不熟悉的端口号
或者也可以使用 iftop 查看是否有占用大带宽的非法程序
sudo apt updatesudo apt install iftop安装之后
sudo iftop -i eth0 -P # 看看是哪个端口在吃掉你的总带宽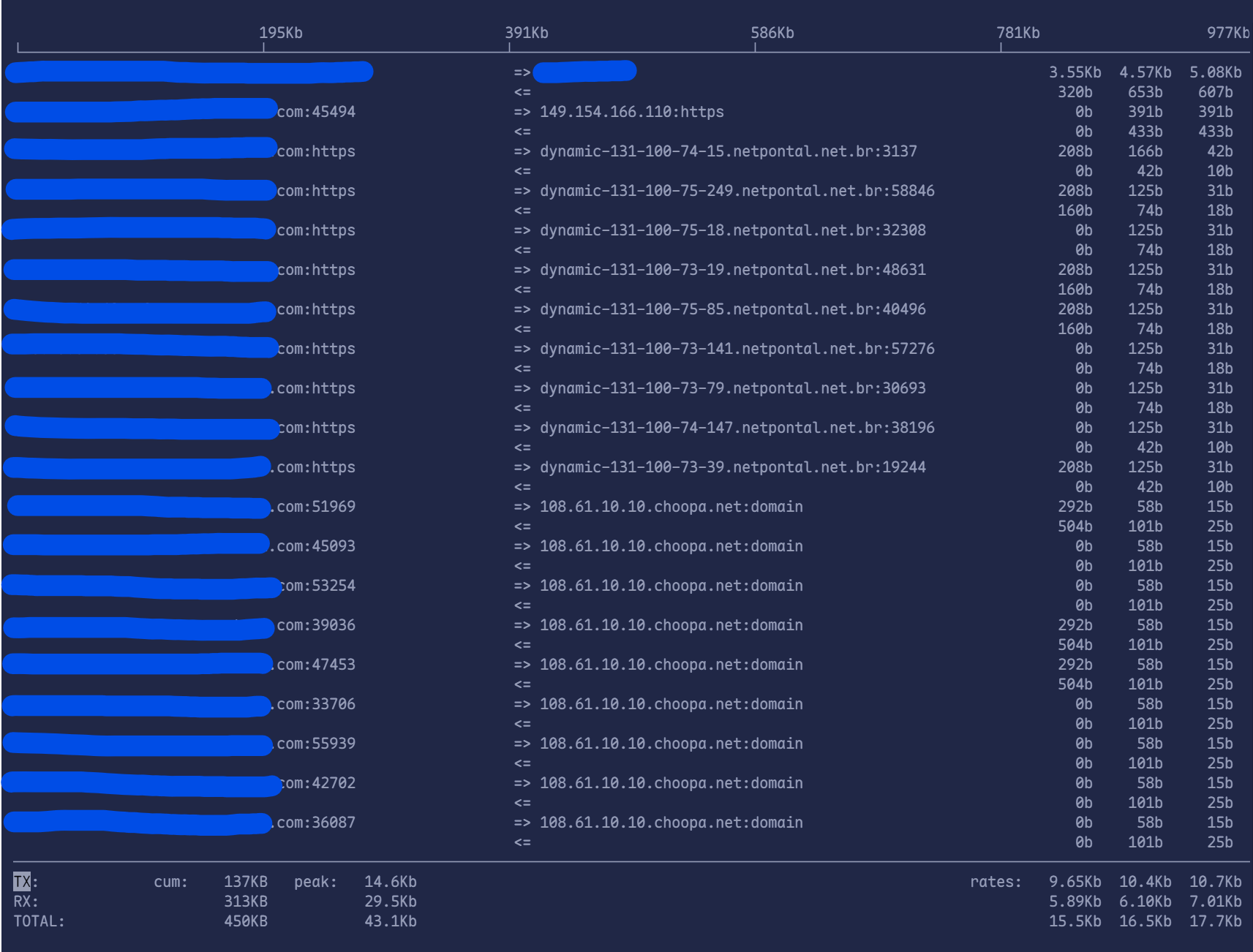
可以看到,这张截图上没有很大带宽的流量,最大的带宽是当前的 SSH 终端。 但是有许多大量的、来自 *.netpontal.net.br 的连接,从地址可以看出这是一个巴西的 ISP,每个连接的流量极小(只有 208b 或 125b)。这正是 SYN Flood(半连接攻击) 的典型表现:攻击者不发送实际数据,只发送微小的握手请求包来占满你的系统资源
此时我们可以采取以下操作:
屏蔽巴西网段
Terminal window sudo iptables -I INPUT -s 131.100.0.0/16 -j DROP开启抗攻击内核参数
Terminal window sudo sysctl -w net.ipv4.tcp_syncookies=1
3. 自启动
3.1 环境变量
首先检查是否有异常的环境变量
# 检查当前环境变量是否有可疑路径(如 /tmp 或隐藏目录)env# 检查关键配置文件是否有异常的 export 指令cat ~/.bashrc ~/.profile /etc/profile /etc/bash.bashrc | grep "export"# 如果发现可疑项,直接用 vim 编辑对应文件删除该行3.2 定时任务和自启脚本
# 查看并清理用户的定时任务crontab -lcrontab -r # 如果确认全是恶意任务,可直接清空
# 检查系统级定时任务目录ls -la /etc/cron.*ls -la /var/spool/cron/crontabs
# 查看所有正在运行的可疑服务systemctl list-units --type=service --state=running# 停止并禁用可疑服务(以 anubis 为例)systemctl stop anubissystemctl disable anubis# 删除服务定义文件rm -f /etc/systemd/system/anubis.servicesystemctl daemon-reload3.3 检查陌生用户
检查是否被创建了具有 Root 权限的新账户
# 检查 UID 为 0(管理员权限)的所有用户awk -F: '$3==0 {print $1}' /etc/passwd# 检查具有登录权限(非 nologin)的用户grep -E "sh$|bash$" /etc/passwd# 如果发现陌生用户(如 hacker123),立即删除其密码或删除用户userdel -r 陌生用户名3.4 检查隐藏进程
# 查找不在 ps 列表中但在 /proc 里的进程 (需要安装 unhide)sudo apt install unhide -ysudo unhide quick reverse# 检查有没有诡异的临时文件系统挂载mount | grep "tmpfs"3.5 检查 LD 相关内容(动态库劫持)
这是非常隐蔽的手段,通过劫持系统库让所有命令都失效
# 检查最重要的预加载文件(正常情况下该文件应为空或不存在)cat /etc/ld.so.preload# 检查环境变量中的预加载echo $LD_PRELOAD# 如果文件中有内容且你不认识,立即清空它: > /etc/ld.so.preload3.6 检查内核有没有被修改
裸金属服务器如果被植入内核模块,普通的 ps 就彻底废了
# 列出已加载的内核模块,寻找名字随机或可疑的模块lsmod# 查看内核日志,寻找有关 "module tainted" 或异常的输出dmesg | grep -iE "tainted|module|hidden"# 验证内核签名(取决于发行版)uname -a3.7 使用专业工具检测 Rootkits 进行检查
首先安装
sudo apt updatesudo apt install rkhunter chkrootkit -y然后运行 chkrootkit
sudo chkrootkit | grep INFECTED之后运行 rkhunter
sudo rkhunter --updatesudo rkhunter --check --sk # --sk 表示自动确认,无需手动回车$ sudo rkhunter --check --sk[ Rootkit Hunter version 1.4.6 ]
Checking system commands...
Performing 'strings' command checks Checking 'strings' command [ OK ]
Performing 'shared libraries' checks Checking for preloading variables [ None found ] Checking for preloaded libraries [ None found ] Checking LD_LIBRARY_PATH variable [ Not found ]
Performing file properties checks Checking for prerequisites [ OK ] /usr/local/sbin/sshd [ OK ] /usr/local/bin/ssh [ OK ] /usr/sbin/adduser [ OK ] /usr/sbin/chroot [ OK ] /usr/sbin/cron [ OK ] /usr/sbin/depmod [ OK ] /usr/sbin/fsck [ OK ] /usr/sbin/groupadd [ OK ] /usr/sbin/groupdel [ OK ] /usr/sbin/groupmod [ OK ] /usr/sbin/grpck [ OK ] /usr/sbin/ifconfig [ OK ] /usr/sbin/ifdown [ OK ] /usr/sbin/ifup [ OK ] /usr/sbin/init [ OK ] /usr/sbin/insmod [ OK ] /usr/sbin/ip [ OK ] /usr/sbin/lsmod [ OK ] /usr/sbin/modinfo [ OK ] /usr/sbin/modprobe [ OK ] /usr/sbin/nologin [ OK ] /usr/sbin/pwck [ OK ] /usr/sbin/rmmod [ OK ] /usr/sbin/route [ OK ] /usr/sbin/rsyslogd [ OK ] /usr/sbin/runlevel [ OK ] /usr/sbin/sshd [ OK ] /usr/sbin/sulogin [ OK ] /usr/sbin/sysctl [ OK ] /usr/sbin/useradd [ OK ] /usr/sbin/userdel [ OK ] /usr/sbin/usermod [ OK ] /usr/sbin/vipw [ OK ] /usr/sbin/unhide [ OK ] /usr/sbin/unhide-linux [ OK ] /usr/sbin/unhide-posix [ OK ] /usr/sbin/unhide-tcp [ OK ] /usr/bin/awk [ OK ] /usr/bin/basename [ OK ] /usr/bin/bash [ OK ] /usr/bin/cat [ OK ] /usr/bin/chattr [ OK ] /usr/bin/chmod [ OK ] /usr/bin/chown [ OK ] /usr/bin/cp [ OK ] /usr/bin/curl [ OK ] /usr/bin/cut [ OK ] /usr/bin/date [ OK ] /usr/bin/df [ OK ] /usr/bin/diff [ OK ] /usr/bin/dirname [ OK ] /usr/bin/dmesg [ OK ] /usr/bin/dpkg [ OK ] /usr/bin/dpkg-query [ OK ] /usr/bin/du [ OK ] /usr/bin/echo [ OK ] /usr/bin/egrep [ Warning ] /usr/bin/env [ OK ] /usr/bin/fgrep [ Warning ] /usr/bin/file [ OK ] /usr/bin/find [ OK ] /usr/bin/fuser [ OK ] /usr/bin/grep [ OK ] /usr/bin/groups [ OK ] /usr/bin/head [ OK ] /usr/bin/id [ OK ] /usr/bin/ip [ OK ] /usr/bin/ipcs [ OK ] /usr/bin/kill [ OK ] /usr/bin/killall [ OK ] /usr/bin/last [ OK ] /usr/bin/lastlog [ OK ] /usr/bin/ldd [ OK ] /usr/bin/less [ OK ] /usr/bin/logger [ OK ] /usr/bin/login [ OK ] /usr/bin/ls [ OK ] /usr/bin/lsattr [ OK ] /usr/bin/lsmod [ OK ] /usr/bin/lsof [ OK ] /usr/bin/mail [ OK ] /usr/bin/md5sum [ OK ] /usr/bin/mktemp [ OK ] /usr/bin/more [ OK ] /usr/bin/mount [ OK ] /usr/bin/mv [ OK ] /usr/bin/netstat [ OK ] /usr/bin/newgrp [ OK ] /usr/bin/passwd [ OK ] /usr/bin/perl [ OK ] /usr/bin/pgrep [ OK ] /usr/bin/ping [ OK ] /usr/bin/pkill [ OK ] /usr/bin/ps [ OK ] /usr/bin/pstree [ OK ] /usr/bin/pwd [ OK ] /usr/bin/readlink [ OK ] /usr/bin/rkhunter [ OK ] /usr/bin/runcon [ OK ] /usr/bin/sed [ OK ] /usr/bin/sh [ OK ] /usr/bin/sha1sum [ OK ] /usr/bin/sha224sum [ OK ] /usr/bin/sha256sum [ OK ] /usr/bin/sha384sum [ OK ] /usr/bin/sha512sum [ OK ] /usr/bin/size [ OK ] /usr/bin/sort [ OK ] /usr/bin/ssh [ OK ] /usr/bin/stat [ OK ] /usr/bin/strace [ OK ] /usr/bin/strings [ OK ] /usr/bin/su [ OK ] /usr/bin/sudo [ OK ] /usr/bin/tail [ OK ] /usr/bin/telnet [ OK ] /usr/bin/test [ OK ] /usr/bin/top [ OK ] /usr/bin/touch [ OK ] /usr/bin/tr [ OK ] /usr/bin/uname [ OK ] /usr/bin/uniq [ OK ] /usr/bin/users [ OK ] /usr/bin/vmstat [ OK ] /usr/bin/w [ OK ] /usr/bin/watch [ OK ] /usr/bin/wc [ OK ] /usr/bin/wget [ OK ] /usr/bin/whatis [ OK ] /usr/bin/whereis [ OK ] /usr/bin/which [ Warning ] /usr/bin/who [ OK ] /usr/bin/whoami [ OK ] /usr/bin/numfmt [ OK ] /usr/bin/kmod [ OK ] /usr/bin/systemd [ OK ] /usr/bin/systemctl [ OK ] /usr/bin/mawk [ OK ] /usr/bin/mail.mailutils [ OK ] /usr/bin/dash [ OK ] /usr/bin/x86_64-linux-gnu-size [ OK ] /usr/bin/x86_64-linux-gnu-strings [ OK ] /usr/bin/telnet.netkit [ OK ] /usr/bin/w.procps [ OK ] /usr/lib/systemd/systemd [ OK ]
Checking for rootkits...
Performing check of known rootkit files and directories 55808 Trojan - Variant A [ Not found ] ADM Worm [ Not found ] AjaKit Rootkit [ Not found ] Adore Rootkit [ Not found ] aPa Kit [ Not found ] Apache Worm [ Not found ] Ambient (ark) Rootkit [ Not found ] Balaur Rootkit [ Not found ] BeastKit Rootkit [ Not found ] beX2 Rootkit [ Not found ] BOBKit Rootkit [ Not found ] cb Rootkit [ Not found ] CiNIK Worm (Slapper.B variant) [ Not found ] Danny-Boy's Abuse Kit [ Not found ] Devil RootKit [ Not found ] Diamorphine LKM [ Not found ] Dica-Kit Rootkit [ Not found ] Dreams Rootkit [ Not found ] Duarawkz Rootkit [ Not found ] Ebury backdoor [ Not found ] Enye LKM [ Not found ] Flea Linux Rootkit [ Not found ] Fu Rootkit [ Not found ] Fuck`it Rootkit [ Not found ] GasKit Rootkit [ Not found ] Heroin LKM [ Not found ] HjC Kit [ Not found ] ignoKit Rootkit [ Not found ] IntoXonia-NG Rootkit [ Not found ] Irix Rootkit [ Not found ] Jynx Rootkit [ Not found ] Jynx2 Rootkit [ Not found ] KBeast Rootkit [ Not found ] Kitko Rootkit [ Not found ] Knark Rootkit [ Not found ] ld-linuxv.so Rootkit [ Not found ] Li0n Worm [ Not found ] Lockit / LJK2 Rootkit [ Not found ] Mokes backdoor [ Not found ] Mood-NT Rootkit [ Not found ] MRK Rootkit [ Not found ] Ni0 Rootkit [ Not found ] Ohhara Rootkit [ Not found ] Optic Kit (Tux) Worm [ Not found ] Oz Rootkit [ Not found ] Phalanx Rootkit [ Not found ] Phalanx2 Rootkit [ Not found ] Phalanx2 Rootkit (extended tests) [ Not found ] Portacelo Rootkit [ Not found ] R3dstorm Toolkit [ Not found ] RH-Sharpe's Rootkit [ Not found ] RSHA's Rootkit [ Not found ] Scalper Worm [ Not found ] Sebek LKM [ Not found ] Shutdown Rootkit [ Not found ] SHV4 Rootkit [ Not found ] SHV5 Rootkit [ Not found ] Sin Rootkit [ Not found ] Slapper Worm [ Not found ] Sneakin Rootkit [ Not found ] 'Spanish' Rootkit [ Not found ] Suckit Rootkit [ Not found ] Superkit Rootkit [ Not found ] TBD (Telnet BackDoor) [ Not found ] TeLeKiT Rootkit [ Not found ] T0rn Rootkit [ Not found ] trNkit Rootkit [ Not found ] Trojanit Kit [ Not found ] Tuxtendo Rootkit [ Not found ] URK Rootkit [ Not found ] Vampire Rootkit [ Not found ] VcKit Rootkit [ Not found ] Volc Rootkit [ Not found ] Xzibit Rootkit [ Not found ] zaRwT.KiT Rootkit [ Not found ] ZK Rootkit [ Not found ]
Performing additional rootkit checks Suckit Rootkit additional checks [ OK ] Checking for possible rootkit files and directories [ None found ] Checking for possible rootkit strings [ None found ]
Performing malware checks Checking running processes for suspicious files [ None found ] Checking for login backdoors [ None found ] Checking for sniffer log files [ None found ] Checking for suspicious directories [ None found ] Checking for suspicious (large) shared memory segments [ None found ] Checking for Apache backdoor [ Not found ]
Performing Linux specific checks Checking loaded kernel modules [ OK ] Checking kernel module names [ OK ]
Checking the network...
Performing checks on the network ports Checking for backdoor ports [ None found ]
Performing checks on the network interfaces Checking for promiscuous interfaces [ None found ]
Checking the local host...
Performing system boot checks Checking for local host name [ Found ] Checking for system startup files [ Found ] Checking system startup files for malware [ None found ]
Performing group and account checks Checking for passwd file [ Found ] Checking for root equivalent (UID 0) accounts [ None found ] Checking for passwordless accounts [ None found ] Checking for passwd file changes [ None found ] Checking for group file changes [ None found ] Checking root account shell history files [ OK ]
Performing system configuration file checks Checking for an SSH configuration file [ Found ] Checking if SSH root access is allowed [ Warning ] Checking if SSH protocol v1 is allowed [ Not set ] Checking for other suspicious configuration settings [ None found ] Checking for a running system logging daemon [ Found ] Checking for a system logging configuration file [ Found ] Checking if syslog remote logging is allowed [ Not allowed ]
Performing filesystem checks Checking /dev for suspicious file types [ None found ] Checking for hidden files and directories [ None found ]
System checks summary=====================
File properties checks... Files checked: 145 Suspect files: 3
Rootkit checks... Rootkits checked : 499 Possible rootkits: 0
Applications checks... All checks skipped
The system checks took: 47 seconds
All results have been written to the log file: /var/log/rkhunter.log
One or more warnings have been found while checking the system.Please check the log file (/var/log/rkhunter.log)三、防护措施
防火墙
安装最新最热防火墙管理工具 nftables
sudo apt updatesudo apt install nftables -y因为新版 Debian/Ubuntu 系统已经就是用着“套皮” nftables 来管理防火墙,所以即使你安装的是新的软件,但是之前的防火墙配置也还在这上面
我们可以通过下面的命令来查看之前的表
sudo nft list ruleset$ # sudo nft list rulesettable ip filter { chain INPUT { type filter hook input priority 0; policy accept; ip saddr 131.100.0.0/16 counter packets 1749 bytes 90936 drop meta l4proto tcp counter packets 167212 bytes 122373248 jump f2b-sshd }
chain FORWARD { type filter hook forward priority 0; policy drop; counter packets 6149938 bytes 3213518507 jump DOCKER-USER counter packets 6149938 bytes 3213518507 jump DOCKER-ISOLATION-STAGE-1 oifname "docker0" ct state related,established counter packets 3149324 bytes 1617411443 accept oifname "docker0" counter packets 44958 bytes 2615072 jump DOCKER iifname "docker0" oifname != "docker0" counter packets 2955656 bytes 1593491992 accept iifname "docker0" oifname "docker0" counter packets 0 bytes 0 accept }
chain OUTPUT { type filter hook output priority 0; policy accept; }
chain DOCKER { iifname != "docker0" oifname "docker0" meta l4proto tcp ip daddr 172.17.0.2 tcp dport 9000 counter packets 41060 bytes 2399884 accept iifname != "docker0" oifname "docker0" meta l4proto tcp ip daddr 172.17.0.3 tcp dport 1935 counter packets 3898 bytes 215188 accept }
chain DOCKER-ISOLATION-STAGE-1 { iifname "docker0" oifname != "docker0" counter packets 2955656 bytes 1593491992 jump DOCKER-ISOLATION-STAGE-2 counter packets 6149938 bytes 3213518507 return }
chain DOCKER-ISOLATION-STAGE-2 { oifname "docker0" counter packets 0 bytes 0 drop counter packets 2955656 bytes 1593491992 return }
chain DOCKER-USER { counter packets 6149938 bytes 3213518507 return }
chain f2b-sshd { ip saddr 124.237.79.34 counter packets 0 bytes 0 reject ip saddr 195.24.237.3 counter packets 16 bytes 960 reject counter packets 167196 bytes 122372288 return }}table ip nat { chain PREROUTING { type nat hook prerouting priority -100; policy accept; fib daddr type local counter packets 23720414 bytes 1281011871 jump DOCKER }
chain INPUT { type nat hook input priority 100; policy accept; }
chain POSTROUTING { type nat hook postrouting priority 100; policy accept; oifname != "docker0" ip saddr 172.17.0.0/16 counter packets 20051 bytes 1224503 masquerade meta l4proto tcp ip saddr 172.17.0.2 ip daddr 172.17.0.2 tcp dport 9000 counter packets 0 bytes 0 masquerade meta l4proto tcp ip saddr 172.17.0.3 ip daddr 172.17.0.3 tcp dport 1935 counter packets 0 bytes 0 masquerade }
chain OUTPUT { type nat hook output priority -100; policy accept; ip daddr != 127.0.0.0/8 fib daddr type local counter packets 22 bytes 1315 jump DOCKER }
chain DOCKER { iifname "docker0" counter packets 0 bytes 0 return iifname != "docker0" meta l4proto tcp tcp dport 9000 counter packets 41060 bytes 2399884 dnat to 172.17.0.2:9000 iifname != "docker0" meta l4proto tcp tcp dport 1935 counter packets 3898 bytes 215188 dnat to 172.17.0.3:1935 }}可以看到它自带一个 filter 表,并且我们刚刚通过 fail2ban 封掉的 IP 也在这个上面
我们现在只对外开放 22 (SSH) 和 80, 443 的 HTTP(S) 服务的端口号,尽可能减小通过弱端口的攻击
# 1. 允许已建立的连接(确保你的机器人发请求能收到回包)sudo nft add rule ip filter INPUT ct state established,related accept
# 2. 允许本地回环(系统内部通信必须)sudo nft add rule ip filter INPUT iifname "lo" accept
# 3. 明确放行你的核心端口sudo nft add rule ip filter INPUT tcp dport 22 accept # 这里的 22 修改成你的 SSH 端口号sudo nft add rule ip filter INPUT tcp dport { 80, 443 } accept
# 4. 修改默认策略为 DROP (丢弃所有未被允许的入站流量)# 注意:这一步执行后,除了 22, 80, 443,其他所有端口在外部都将无法访问sudo nft "chain ip filter INPUT { policy drop ; }"基本可以防护的部分也就只有防火墙来阻挡未知 IP 来访问端口了,再者就是定期做检查
四、总结
自己的网络安全自己负责,不要因为自己的安全意识淡薄去给别人造成麻烦。 网络攻击是逐年在增加的,且手段越来越丰富,有了 AI 的加持会让很多原来不会攻击的人也参与到攻击。 所以,不要对任何服务的暴露与脚本使用报侥幸心理。
- 不用的服务尽量关闭。
- 不要给普通用户设置
sudo免密。 - 做好权限隔离,给对外的服务。